Is Using Public WiFi safe?
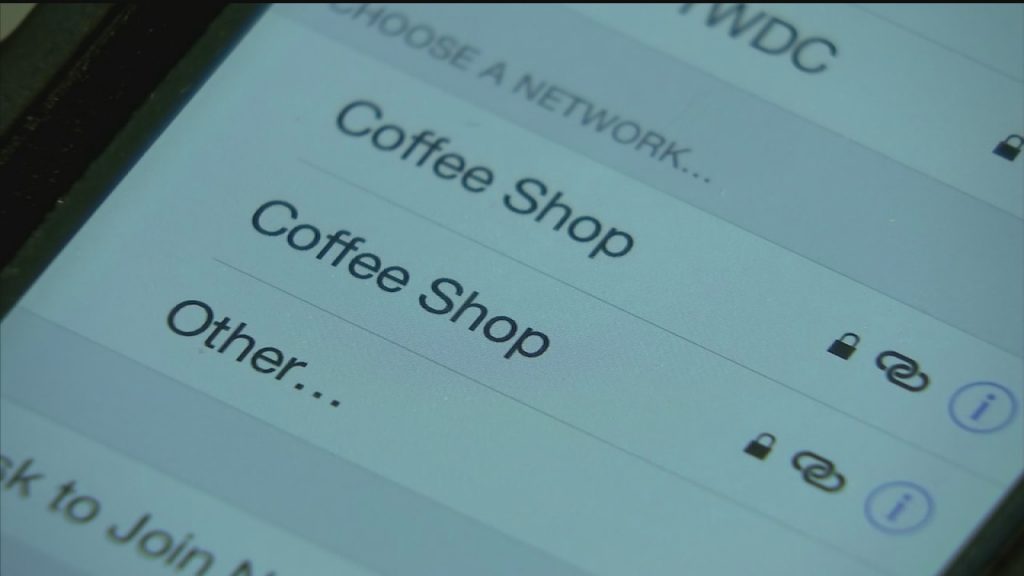
Free Wifi is available in coffee shops, restaurants, shopping malls, hotels, airports, libraries -you name it. Millions of people everyday use this doing everything from browsing the internet, checking emails, and just any internet related tasks. Although, most people do not realize even though there is a password to login, free public Wi-Fi is not […]
iProtection
What is the first thing you grab when you wake up in the morning? Most people would answer this question by saying, their smartphone. Statistics state that an average smartphone user checks their device almost 47 times a day and checks their device within the first hour of waking up or before going to bed. […]
Apple Scam Alert!
Apple Scam Alert: There is a phishing scam that has been out for a while which actually spoofs Apple Inc. and it is designed to hoodwink you. It comes in the form of a phone call and/or email. It can start with an ‘automated’ phone call that display’s Apple’s logo, address and real phone number, warning about […]
Rackspace – Resetting the root user password from rescue mode
I was searching for these instructions the other day as I’ve almost never had success resetting the root password from Rackspace’s GUI. Since Rackspace suddenly decided not to host a community forum anymore (whhyyyy?!) we’re posting these original instructions here for those that need the reference: Resetting the root user password from rescue mode Thank […]
Symposit modernizes DC consulting firm’s network using Ubiquiti SDN
[siteorigin_widget class=”WP_Widget_Media_Gallery”][/siteorigin_widget] Challenge: The client requested that Symposit assess the internal network and to modernize it in order to make it more secure, manageable, and of course faster. Since there was no one to properly manage the network, there was no visibility and hence no security within the network. Additionally, the aging network stack was […]
US Govt Tracking Sheet for Foreign Tech Companies
We have created the Google sheet for tracking purposes as it relates to the recent slew of foreign technology companies that have been barred or are considered being barred from use by the US Government, either by one or multiple agencies. Commercial and private sector organizations may want to consider this guidance as well when […]
Symposit Founder, Bobby Bermudez, to serve on Board of Directors for Byte Back
WASHINGTON D.C. Symposit LLC President and Founder, Bobby Bermudez, was recently appointed to the Board of Directors for Byte Back, a D.C. based non-profit with a mission to improve economic opportunity by providing computer training and career preparation to under-served Washington, DC metro area residents. By serving on the Board, Bobby will actively help play a […]
Control your privacy by managing advertising choices.
One of the best ways to manage your privacy is to manage and opt-out of advertising personalization settings for the browser that you most frequently use. This is especially helpful on mobile devices where targeted ads will annoy you and potentially expose your personal habits to marketers and ad agencies. Today we will share some […]
ONLINE SECURITY – What can you do to become more vigilant?
ONLINE SECURITY – What can you do to become more vigilant? This the first, in series of Blog posts, to help you with identifying the threats and current redirect practices being conducted by online scammers. One of the tactics that online scammers are using to try to fool people into visiting malicious websites is a […]
CCleaner’s argument for open source
For many, many years we have lauded the use of CCleaner to clean and optimize Windows based workstations in many different environments. Unfortunately our stance is changing today. Security researchers at Cisco Talos discovered that the 32-bit version of CCleaner 5.33 was triggering alerts on their advanced malware protection systems. They found that malware was bundled […]