Is Using Public WiFi safe?
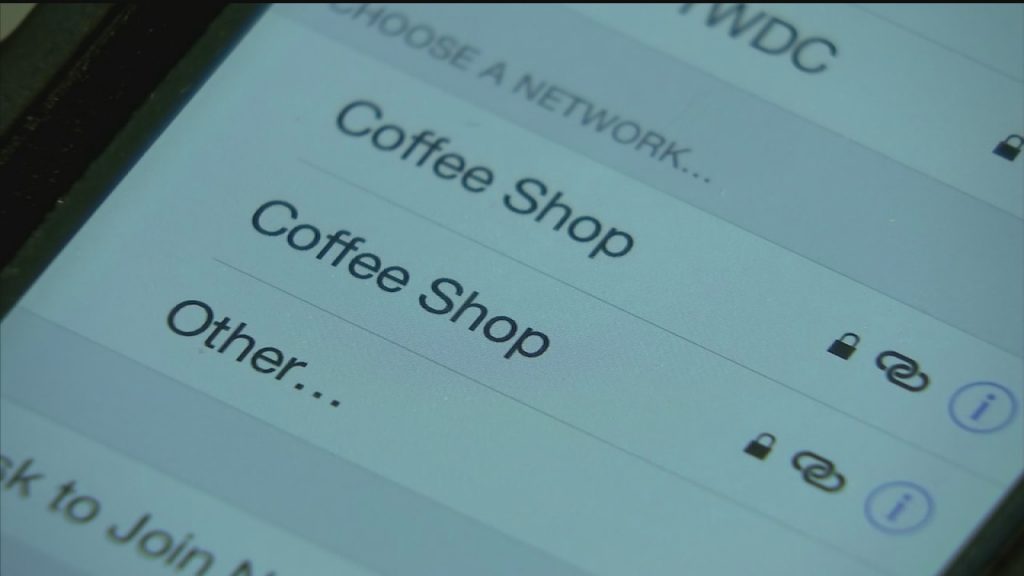
Free Wifi is available in coffee shops, restaurants, shopping malls, hotels, airports, libraries -you name it. Millions of people everyday use this doing everything from browsing the internet, checking emails, and just any internet related tasks. Although, most people do not realize even though there is a password to login, free public Wi-Fi is not […]
Formjacking?

What is Formjacking? This is not a new form of cyber attack, but it has recently increased since the past year. It is form of JavaScript-code where cyber criminals hack and take control over the functionality of the site’s form page. This malicious JavaScript code is used to steal credit card details and payment form […]
IRS Scam Alert!
ATTENTION! ATTENTION! As April 15th approaches and many are stressed and worried about filing their taxes to the IRS. Although many people take this time of the year seriously, there are people who see this as a way to scam people out of money. It usually starts with a random phone call from a person […]
Protect your network by implementing DNSCrypt
The Internet Domain Name System (DNS) is truly amazing technology – without it, you wouldn’t be able to type in google.com and reach your destination. DNS was created to assist humans in having an easy address to remember server IP addresses. Think of it as knowing a street address instead of remembering the longitudinal coordinates […]
Be secure, adopt “less is more.”
I’d like to talk about something very important with regards to computer security, and really computing in general. Computers are indeed complex machines, with many layers of working components working in tandem to present you with a useful and useable experience. Each one of the aforementioned “components” is a potential attack vector for an attacker. […]
Protect yourself by using disposable information
How many times a day do you give out your email address, inadvertently or voluntarily? How many lists do you think your email address appears on? Can you trust every vendor you register with? I know I would have a tough time answering these questions. Of course, I tend to be a rather private person […]
Importance of using two-factor authentication
You’ve heard it before, but I’ll say it here again. The web, including your data, is under constant attack. Everywhere and all the time. Some of the attacks are automated and come from “robots,” while others are actual humans trying to break in. Failing to utilize two-factor authentication, whereever and whenever possible, will leave you exposed. […]